
For the Inventor. By the Inventor.
See this week's breakthrough USPTO patent grants!
Market Volatility Exposes Weak Delegation
When markets get shaky, advisors don’t just manage portfolios. They manage fear, questions, follow-up and a flood of client communication.
That’s where weak delegation gets expensive.
If meeting prep, paperwork, CRM updates and account admin still run through you, response times slip and the client experience takes the hit.
BELAY created the free Financial Advisor’s Delegation Guide to help you identify what to hand off, what to keep and how to stay client-facing without losing control.
Inside, you’ll learn how to reduce bottlenecks, protect responsiveness and free up more time for the work only you should be doing.
Table of Contents
New weekly USPTO Patents data have been added.
Cited by Wikipedia as a comprehensive source for global prolific inventors.
Top Inventors:
Peter Russell-Clarke - 11
Tao Luo - 11
M. Evans Hankey - 10
Duncan Robert Kerr - 10
Shota Aoyagi - 9
Benjamin Andrew Shaffer - 9
Jonathan P. Ive - 9
Xiaoxia Zhang - 9
Bartley K. Andre - 7
Richard P. Howarth - 7
Eugene Antony Whang - 7
Rico Zörkendörfer - 7
William H. Eby - 7
Yan Zhou - 7
Want your company featured to 50,000 plus innovation-minded readers? Sponsor an IDiyas story. Please see our newsletter stats. Send us an email to: [email protected] for details.
🔑 Public Key Cryptography: The Geeky Handshake That Secures the Internet
Because whispering your bank password in a crowded café just wasn’t scalable
Before the 1970s, if you wanted to send a secret message, your best bet was to meet in a shadowy alley and exchange a private key while pretending you were in a spy movie. Effective, yes. Scalable? Not so much.
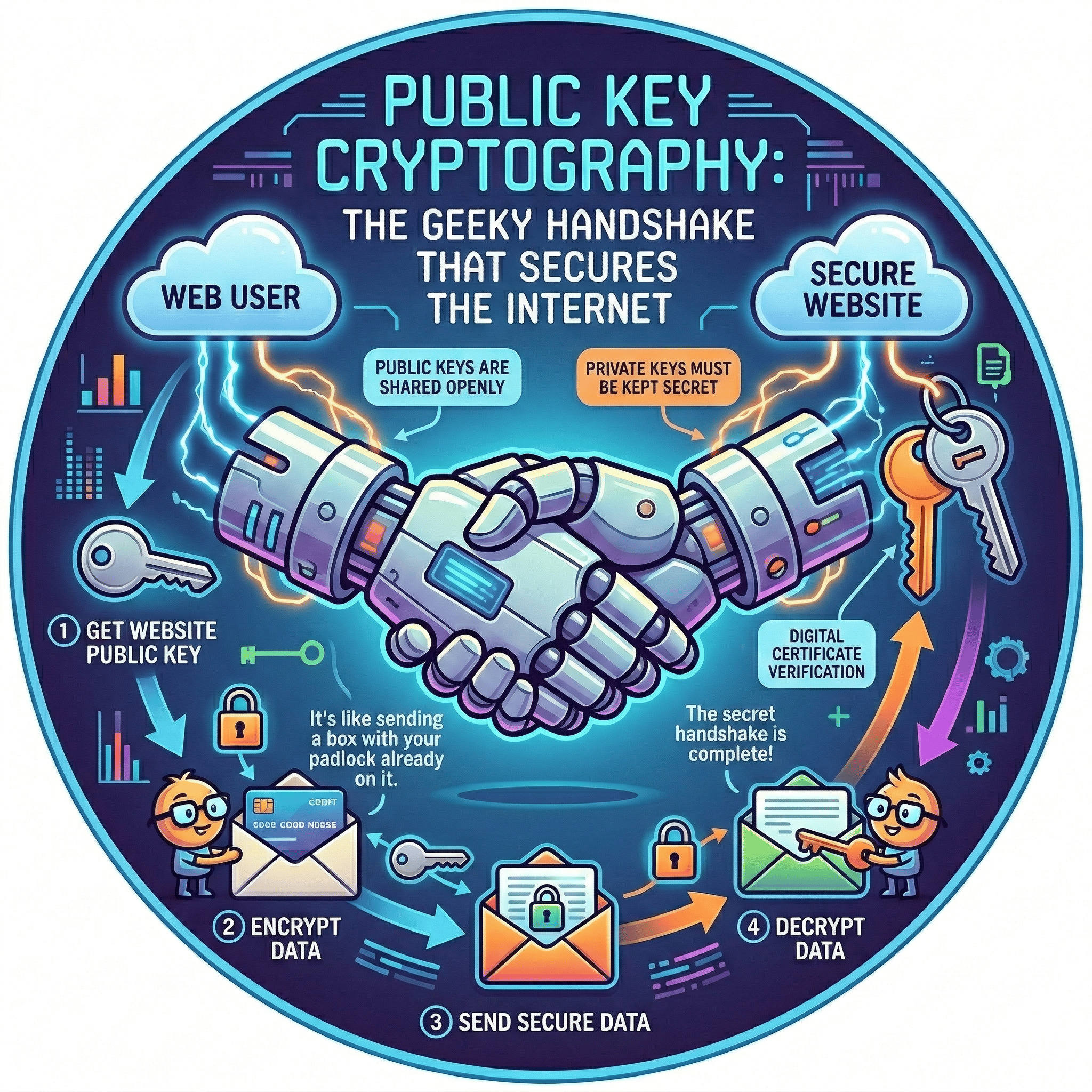
Enter the unlikely heroes of the digital security saga: Whitfield Diffie, Martin Hellman, and a few other brilliant minds with excellent patience for math. They introduced something revolutionary: public key cryptography, the ultimate socially-distanced handshake.
Here’s the genius: Instead of both parties needing the same key (like a shared diary lock), public key cryptography lets you share your lock with the world, while keeping the key hidden in your pocket. People can lock messages to you, but only you can unlock them. It’s like everyone having a mailbox anyone can drop into, but only you have the key to open it.
This clever system now underpins just about everything you do online:
🛒 Online shopping
📧 Secure emails
🏦 Online banking
🕵️ VPNs for private browsing (or pretending you’re in Switzerland to watch better Netflix)
Without it, the internet would be a digital Wild West, wide open, full of bandits, and probably password-protected by “1234.”
So next time you log into your bank or send a sensitive message, spare a grateful thought for the mathematicians who made it possible: Diffie, Hellman, and the quiet army of cryptographers who ensured you don’t need a trench coat to keep secrets anymore.
🔐 Want more behind-the-scenes brilliance? Subscribe to IDiyas and meet the minds who make our modern world click, clack, and encrypt.
Advertisement
Private Credit on Your Terms
Percent's secondary marketplace lets accredited investors buy into eligible deals or indicate interest in selling existing positions. Secondary market access in private credit is still rare. 16.72% current weighted average coupon. Terms start at 3 months. New investors can receive up to $500 credit.
Alternative investments are speculative. Secondary liquidity not guaranteed. Past performance not indicative. Terms apply.
Trivia
As of 2026, which of these is officially required by the USPTO to name a "natural person" as an inventor on an AI-assisted patent?
A) The AI must have its own digital signature.
B) A human must have provided "significant contribution" to every claim.
C) The AI must be registered as a "Joint Inventor."
Please scroll to the bottom of this newsletter to find out.
Featured Inventor
The Hacker Who Taught the World to Speak: Severin Hacker and the Code Behind Duolingo
In the world of language learning, few names carry the quiet precision and global impact of Severin Hacker, and yes, that is his real name, which makes him arguably the most benign hacker to ever reshape human communication.
Born in Switzerland and forged in the halls of ETH Zurich and Carnegie Mellon University, Hacker has always straddled two worlds: the rigorous logic of machine learning and the messy, beautiful chaos of human language.

After completing his BS in Computer Science at ETH Zurich in 2006, he dove into a Ph.D. at Carnegie Mellon, researching large-scale human computation under the mentorship of Luis von Ahn, the same man who once made you type blurry words to prove you're not a robot (CAPTCHA) and who later co-founded Duolingo with Hacker in 2011.
Their idea was both radical and refreshingly obvious: create a language learning platform that’s free, fun, and driven by data. Severin, now Duolingo’s Chief Technology Officer, became the architect of its intelligent backend, the code that decides which Spanish verb you’ve mastered and which one will haunt you in tomorrow’s practice session.
Under his technological stewardship, Duolingo grew from a quirky app into a global platform with over half a billion users and more than 40 languages, from French to Klingon. For his work, Hacker received the MIT Technology Review TR35 Award in 2014, recognizing him as one of the world’s top innovators under 35.
Quietly brilliant and fluently methodical, Severin Hacker didn’t just help build an app, he built an algorithmic bridge between people, cultures, and the future of education.
Today in Patent History
🚙 The Jeep’s "Stolen" Legacy: Innovation, War, and the 1942 Patent 🎖️
On this date in 1942, the Jeep patent was issued. While Colonel Byron Q. Jones is listed, Karl Probst of Bantam Car Company is the true inventor. The Army later sidelined Bantam for Ford and Willys-Overland to meet WWII demand, producing 650,000 units. Though "Jeep" likely stemmed from WWI slang rather than "GP" (General Purpose), it remains an iconic global trademark, now a cornerstone of the Stellantis portfolio.

U.S. Patent No. 2,278,450
Advertisement
The IT strategy every team needs for 2026
2026 will redefine IT as a strategic driver of global growth. Automation, AI-driven support, unified platforms, and zero-trust security are becoming standard, especially for distributed teams. This toolkit helps IT and HR leaders assess readiness, define goals, and build a scalable, audit-ready IT strategy for the year ahead. Learn what’s changing and how to prepare.
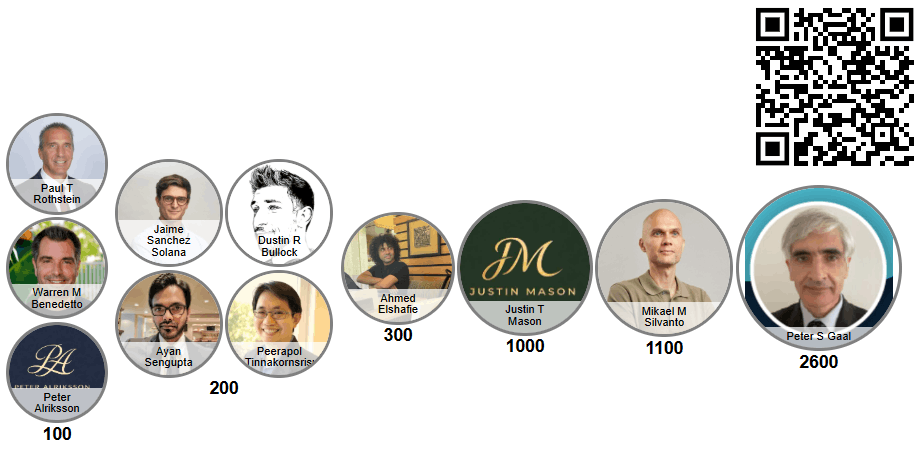
Centurion Patentors
Congratulations to last week's Centurion Patentors! |
The Centurion Patentors are 0.185% of ALL Inventors worldwide who hold more than one hundred U.S. patents. They are the Navy SEALs of innovation. They don’t just have good ideas once; they’ve built a discipline, a repeatable process for turning thought into impact. |
We are excited to welcome the following inventors into these prestigious patent clubs: |
Trivia
Answer: B. (Following the Thaler v. Vidal ruling and 2025/2026 guidance, AI cannot be an inventor; a human must prove they directed the "conception.") ✅
Recommendations
You may want to signup to the following newsletters:

Sponsored
Private Equity Bros
Sponsored
Haute Impact
Insights from the intersection of luxury, technology, and sustainability.
A century ago, pilots tried refueling mid-air with nothing but a hose… and hope. Today, aerial refueling is the invisible backbone of global military power. From Seversky’s 1921 patent to Boeing’s flying boom, this video uncovers the hidden system that keeps aircraft in the sky, and reshapes geopolitics.
Disclosure: Our free newsletter and website may include paid placements (labeled “Sponsored,” “Partnered,” or “Ad”) as well as affiliate links. If you click or make a purchase, we may earn a commission. We are not affiliated with the advertisers featured. These partnerships help us keep the newsletter free for our readers.
Any claims made in advertising content are not researched, verified, or endorsed by IDiyas.



